A research team headed by Professor Hoi-Kwong Lo from the University of Toronto has discovered a new quantum encryption technique to provide protection against the most advanced hackers.
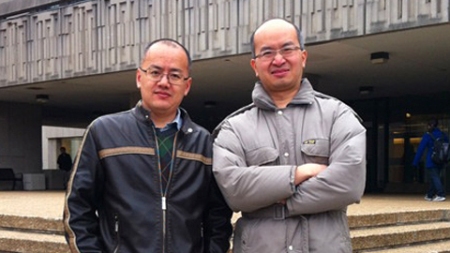 Dr. Bing Qi, Senior Research Associate and Professor Hoi-Kwong Lo of The Edward S. Rogers Sr. Department of Electrical & Computer Engineering and the Department of Physics.
Dr. Bing Qi, Senior Research Associate and Professor Hoi-Kwong Lo of The Edward S. Rogers Sr. Department of Electrical & Computer Engineering and the Department of Physics.
The finding has been reported in the journal, Physical Review Letters. Quantum cryptography is a foolproof method to prevent any attempt of hacking by generating disturbances that can be noticed by legitimate users, thus providing an unconditional protection to encryption key transmission between the users. Light signals are used to transmit the encryption key, which is received utilizing photon detectors. Here, the risk is the chance of interception and manipulation of these signals by a hacker.
According to Dr. Charles Bennett, an IBM research fellow and the co-inventor of quantum cryptography, photon detectors have become a vulnerable point in quantum key distribution (QKD), allowing clever side-channel attacks, called as quantum hacking. If quantum hacking happens, light signals destabilize the photon detectors, thus they can receive only the photons sent by the hacker.
To overcome this problem, Professor Lo’s team has developed a technique named as Measurement Device Independent QKD. This method allows legitimate users to ignore the measurement results transmitted by the hacker by simply validating the hacker’s integrity through the measurement and comparison of their own data. The objective is to find subtle modifications that happen during the manipulation of quantum data by a hacker.
In Measurement Device Independent QKD, the legitimate users transmit their signals to an untrustworthy relay, which might be controlled by the hacker. This relay offers an additional comparison point by performing a combined measurement on the signals. Professor Lo explained that the relay’s detectors can be dynamically malfunctioned without compromising security because the legitimate users can verify the integrity of the relay or the hacker using their own data correlations subsequent to their interaction with either relay or the hacker.
The research team has already completed a proof-of-concept measurement. The team is now working on designing a prototype system based on the Measurement Device Independent QKD technique. The prototype is expected to be ready for use within five years.
Source: http://www.engineering.utoronto.ca